It is understood that the Ministry of industry and information technology recently issued the 'guidance on promoting the development of the network security industry (Draft)' (hereinafter referred to as the 'draft for comments'). The draft proposes that in the future, it will focus on the construction of common basic platforms such as network security testing and verification, training exercises, equipment safety testing, etc., focusing on the new application scenarios of industrial Internet, Internet of vehicles and Internet of things. Support the construction of network identity authentication system based on commercial password, fingerprint recognition, face recognition and other technologies.
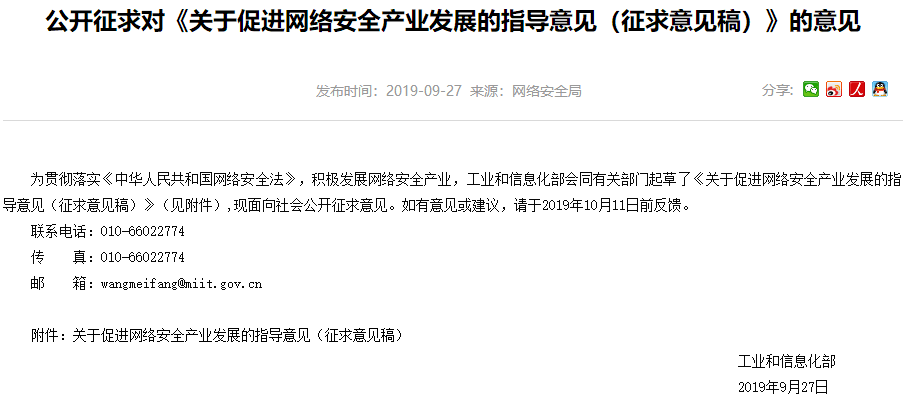
Attached is the full text of the guidance on promoting the development of network security industry (Draft for comments)
Guidance on promoting the development of network security industry
(Draft for comments)
Without network security, there will be no national security, no stable economic and social operation, and it is difficult for the interests of the masses to be protected. At present, various forms of network attacks, hacker intrusion, malicious code, security vulnerabilities emerge in endlessly, which pose a serious threat to the security of key information infrastructure, data security and personal information security. The essence of network security is technology confrontation, which can not be separated from the strong support of network security technology and industry. In recent years, the scale of China's network security industry has grown rapidly, the product system is relatively perfect, the innovation ability is gradually enhanced, and the development environment is obviously optimized. However, compared with the requirements of network security, there are still some problems, such as lack of core technology, small industrial scale, insufficient market demand and insufficient industrial coordination. In order to actively develop the network security industry and improve the technical support level of network security, this guidance is formulated.
1、 General requirements
(1) Guiding ideology
Guided by Xi Jinping's socialist ideology with Chinese characteristics in the new era, we thoroughly implemented the spirit of the series of important speech of general secretary Xi Jinping on network security, persisted in the new development concept, set up the correct network security concept, implemented the network security law, guided by the needs of serving China's Cyberspace Security Strategy, and actively tackled the Internet, big data, artificial intelligence and entities. The new risks associated with the deep economic integration should actively respond to the new challenges brought by the new technologies and new applications such as 5g, industrial Internet, next generation Internet and Internet of things, adhere to the market leading and government guidance, focus on breaking through key technologies, building industrial ecology, optimizing the development environment, and promoting the high-quality development of China's network security industry, so as to maintain the national cyberspace security and ensure the network Powerful country construction provides strong industrial support.
(2) Basic principles
Innovation driven. We will vigorously promote technology and product innovation, break through technical bottlenecks, and strive to enhance the core technical capabilities of network security. We should innovate the network security service mode, improve the professional service level of network security, and realize the transformation of industrial development from product led to service led.
Coordinated development. We should fully mobilize the forces of all parties, strengthen the cooperation of industry, University and research, encourage the transformation of technological achievements, promote the joint and coordinated tackling of key problems by the strong and the strong, and build an industrial ecosystem with multi participation, complementary advantages and integrated development. Promote industry finance cooperation and guide social capital to participate in the development of network security industry.
Demand led. We will continue to increase investment in network security in various industries and fields, adhere to the problem-oriented approach, and strengthen the docking of supply and demand, so as to make the industry better meet the network security needs of key areas such as finance, energy, communication, transportation, e-government.
Open cooperation. One belt, one road, is to promote international exchange and cooperation of network security industry, learn from foreign industrial development mode, promote technology, talent exchange and information sharing, actively participate in the construction of 'one belt and one road' and enhance the international competitiveness of industry.
(3) Development goals
The network security technology innovation ability has been significantly enhanced, the network security products and service system has been more perfect, the network security professional talent team has been growing day by day, the network security industry pattern with the coordinated development of government, industry, University, research and investment has been consolidated, the industrial development environment has been further optimized, and the support capacity of the network security industry in maintaining the national cyberspace security and ensuring the construction of a network power has been greatly improved. By 2025, a number of network security enterprises with an annual revenue of more than 2 billion will be cultivated, and a number of network security backbone enterprises with international competitiveness will be formed. The scale of network security industry will exceed 200 billion.
2、 Main tasks
(1) Strive to break through the key technologies of network security
With the goal of building an advanced and complete network security product system, focusing on the needs of network security pre protection, in-process monitoring, post-processing, investigation and evidence collection, vigorously promote the evolution and upgrading of network security products such as asset identification, vulnerability mining, virus detection, border protection, intrusion prevention, source code detection, data protection, tracing and tracing, and strive to improve the status of hidden danger investigation and status Potential perception, emergency response and traceability. Strengthen the analysis of network security threats and risks in emerging fields such as 5g, next generation Internet, industrial Internet, Internet of things, Internet of vehicles, and vigorously promote the research and development of network security technology products in relevant scenarios. Support the application of cloud computing, big data, artificial intelligence, quantum computing and other technologies in the field of network security, and strive to improve the network security defense capabilities such as threat intelligence analysis, intelligent monitoring and early warning, and encrypted communication. New concepts of network security, such as virtual computing and trust, are actively promoted.
(2) Actively innovate network security service mode
In view of the characteristics of network security, such as strong specialization, rapid technological evolution and difficult application, the concept of 'security as service' is advocated, and network security enterprises are encouraged to change from providing security products to providing security services and solutions. Support professional institutions and enterprises to carry out network security planning consultation, threat intelligence, risk assessment, detection and certification, security integration, emergency response and other security services, and standardize vulnerability scanning and disclosure activities. Support legally established certification bodies to carry out network security certification in accordance with the law. We will vigorously develop the public service platform of network security based on cloud mode, and provide remote real-time online vulnerability detection, website protection, denial of service attack resistance, domain name security and other services. Encourage basic telecom enterprises and cloud service providers to make full use of network resources